Although the island is huge and you can land anywhere, after a few minutes a random circle is overlaid on the map, and a slowly moving wall of deadly energy starts closing in on that circle. Stay outside that circle at your peril; if you find yourself far on the opposite side of the map from a circle, you better start hunting for a vehicle or boat (theyre present, but rare) quickly. These terrordome areas are always shrinking, always impending, in an ever narrowing cone, forcing the remaining survivors closer and closer together. The circles get tighter and deadlier and quicker as the game progresses, ratcheting up the tension and conflict.
Although users have reason to be concerned about their emails being exposed, very few people treat their email address as anything particularly precious these days.
The hashing algorithm. As slow as possible, and ideally designed to beespeciallyslow on GPUs for reasons that will become painfully obvious about 5 paragraphs from now.
When I wrote aboutThe Golden Age of x86 Gaming, Iimpliedthat, in the future, it might be an interesting, albeit expensive, idea to upgrade your video card via an external Thunderbolt 3 enclosure.
If we multiply this effort by 8, and double the amount of time allowed, its conceivable that averymotivated attacker, orone with a sophisticated set of wordlists and masks, could eventually recover 39 16 = 624 passwords, or aboutfive percentof the total users. Thats reasonable, but higher than I would like. We absolutely plan to add a hash type table in future versions of Discourse, so we can switch to an even more secure (read:much slower) password hashing scheme in the next year or two.

Ive said many, many times that the key to becoming an experienced software developer is to understand that you are, at all times,your own worst enemy. I dont mean this in a negative way you have to constantly plan for and design around your inevitable human mistakes and fallibility. Its fundamental to good software engineering because, well, were all human. The good-slash-bad news is that youre onlyaccidentallyout to get yourself. But what happens when were infinitely connected and software is suddenlyeverywhere, in everyones pockets every moment of the day, starting to approximate a natural extension of our bodies? All of a sudden those little collective social software accidents becomeconsiderably more dangerous:
Rememberin 2011when Marc Andreeseen said that Software is eating the world?

In attempting to simplify my answers for an audience of kids, I had concisely articulated the one thing that keeps me coming back to software:to serve man. Not on a platter, for bullshit monetization but software thathelps peoplebe the best version of themselves.
All administrators must have a minimum password length of 15 characters.
There havent been many Battle Royale games, so this game mode is a relatively new phenomenon. If youd like to give it a try for free,I highly recommendFortnites Battle Royale modewhich is 100% free, a near-clone of PUBG, and quite good in its own right.They added their Battle Royale mode well after the fact; the core single player save the world gameplay of building stuff and fighting zombie hordes is quite fun too, though a bit shallow. It also has what is, in my opinion, some of the most outstanding visual style Ive ever seen in a game a cool, hyperbolic cartoon mix of Chuck Jones, Sam & Max, and Cloudy with a Chance of Meatballs. Its also delightfully diverse in its character models.
Yes, thats right, I paid $500 foran external Thunderbolt 3 enclosureto fit a $600 video card, all to enable a plug-in upgrade of a GPU on aSkull Canyon NUCthat itself cost around $1000 fully built. I know, it sounds crazy, and OK fine, I wont argue with you. Its crazy.
@andrewbstilesif it was physically possible to have sex with this TV I.. uh.. Id take it on long, romantic walks
the dread of never knowing when another of the 100 players on this enormous island is going to suddenly appear around a corner or over a hill isintense. Youll find yourself wearing headphones, cranking the volume, constantly on edge listening for the implied threat of footfalls. Wait, did I hear someone just now, or was that me? You clench, and wait. Ive had so many visceral panic moments playing this game, to the point that I had to stop playing just to calm down.
ZWVhZWQ4YjZmODU4Mzc0M2E2ZDRlNjBkNjY3YzE2ODA=

Both backup creation and backup download administrator actions are formally logged.
(The only things youll give up over PUBG are the realistic art style, vehicles, and going prone. But the superb structure building system in Fortnitealmostmakes up for that. If nothing else it is a demonstration of how incredibly compelling the Battle Royale game mode is, because that part of the game iswildly successfulin a a way that the core game, uh, wasnt. Also its free!)
I didnt intend for this to happen, but to me,the Battle Royale game mode perfectly captures the zeitgeist of the current moment, and matches my current state of mind to a disturbing degree. Its an absolutely terrifying experience of every human for themselves, winner takes all, with impossible odds. There are moments it can be thrilling, even inspiring, but mostly its brutal and unforgiving. To succeed you need to be exceedingly cautious, highly skilled, and just plainlucky. Roll the dice again, but know that everyone will run towards the sound of gunfire in hopes of picking off survivors and looting their corpses. Including you.
Ive seenthe Japanese movie, and its true that there werea few Battle Royale gamesbefore PUBG, but this is clearly the defining moment and game for the genre, the one that sets a precedent for everyone else to follow.
Theres a reason every site that reviews TVs had to recalibrate their results whenthey reviewed the 2016 OLED sets.

That game isPlayer Unknowns Battlegrounds. I was increasingly curious why it was so popular, and kept getting more popular every month. Calling it a mere phenomenon seems like underselling it; something truly unprecedented is happening here. I finally broke down and bought a copy for $30 in September.
Its up to you to decide when to drop, and where to land on this huge island, full of incredibly detailed cities, buildings and houses but strangely devoid of all life.
Even with a top of the line GPU thats OK, I guess. Remember this is just one hash were testing against, so youd need one hour per row (user) in the table. And I have more bad news for you: Discourse hasnt allowed 8 character passwords forquite some time now. How long does it take if we try longer numeric passwords?
93LlpbKZKficWfV9jjQNOSp39MT0pDPtYx7/gBLl5jw=
Whats left isthe password hashes. And thats a serious problem indeed.
Im reminded of a particular Mitchell and Webb skit:Are we the baddies?

It should be noted that no ethically-trained software engineer would ever consent to write aDestroyBaghdadprocedure. Basic professional ethics would instead require him to write aDestroyCityprocedure, to which Baghdad could be given as a parameter.
First, a tiny hello world test to see if things are working. I downloadedhashcat. I logged into our demo and created a new account with the password0234567890; I checked the database, and this generated the following values in the hash and salt database columns for that new user:
Lets hashcat it up and see if it works:
My quick hashcat results gave me some confidence that we werent doing anything terribly wrong with the Discourse password hashes stored in the database. But I wanted to becompletely sure, so I hired someone with a background in security and penetration testing to, under a signed NDA, try cracking the password hashes of two live and very popular Discourse siteswe currently host.
Weve read so many sad stories about communities that were fatally compromised or destroyed due to security exploits. We took that lesson to heart when we founded theDiscourseproject; we endeavor to build open source software that is secure and safe for communities by default, even if there are thousands, or millions, of them out there.
?d?d?d?d?d?d?d?d?d [9] Fri Jun 02 10:34:42 2017 (11 hours, 18 mins) ?d?d?d?d?d?d?d?d?d?d [10] Tue Jun 06 17:25:19 2017 (4 days, 18 hours) ?d?d?d?d?d?d?d?d?d?d?d [11] Mon Jul 17 23:26:06 2017 (46 days, 0 hours) ?d?d?d?d?d?d?d?d?d?d?d?d [12] Tue Jul 31 23:58:30 2018 (1 year, 60 days)
Now that the attacker has your database, they can crack your password hashes withlarge scale offline attacks, using the full resources of any cloud they can afford. And once theyve cracked a particular password hash,they can log in as that user forever. Or at least until that user changes their password.

I recently recieved a complimentary copy of the book in the mail. I paged tomy short interview, alongside the very coolKiki Prottsman. I had no real recollection of the interview questions after the months of lead time it takes to print a physical book, but reading the printed page, I suddenly hit myself over the head with the very answer I had been searching my soul for these past 6 months:
Here at the tail end of 2017, from where I sit neither of these jokes seem particularly funny to me any more. Perhaps I have lost the capacity to feel joy as a human being?Haha just kidding!… kinda.
Administrators have a minimum password length of 15 characters.
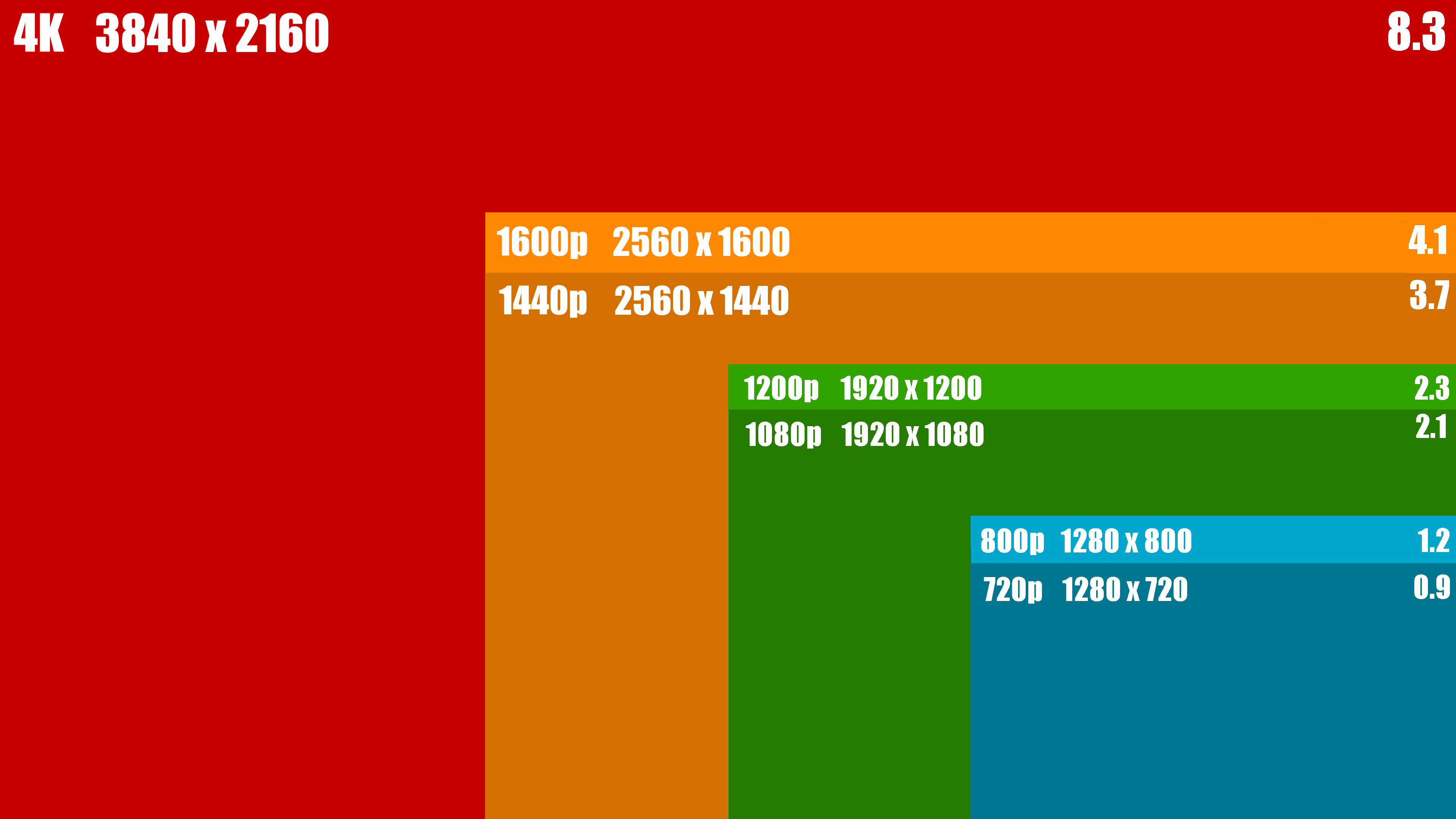
Plain old regular HD, aka 1080p, aka 1920 1080, is one quarter the size of 4k, and ¼ the work. By todays GPU standards HD is pretty mucheasy modethese days. Its not even interesting. No offense to console fans, or anything.
This matters mostly because of 4k, aka 2160p, aka 3840 2160, akaUltra HD.
Late in 2016, I got a4k OLED displayand it kind of blew my mind. I have never seen blacks so black, colors so vivid, on a display so thin. It made my previous 2008 era Panasonic plasma set look lame. Its so good that Im now a little angry that every display that my eyes touch isnt OLED already. I even got into nerd fights over it, and to be honest, Id still throw down for OLED. It is legitimatelythat good. Come at me, bro.

Its hard to explain why Battlegrounds is so compelling, but lets start with the loneliness.
I tried to amplify on these thoughts in recent podcasts:

Users can choose to create a username and password or use various third party authentication mechanisms (Google, Facebook, Twitter, etc). If this option is selected, a secure random 32 character password is autogenerated. It is not possible to know whether any given password is human entered, or autogenerated.
Which is troubling because technically,technically, I run a company thatbuilds comment sections.
Months ago I submitted a brief interview for achildrens book about coding.


Backup download tokens are single use and emailed to the address of the administrator, to confirm that user has full control over the email address.
But that was 4 years ago. Exactly how secure are our password hashes in the database today? Or 4 years from now, or 10 years from now? Were building open source software for the long haul, and we need to be sure we are making reasonable decisions that protect everyone. So in the spirit ofdesigning for evil, its time to put on our Darth Helmet and play the bad guy lets crack our own hashes!
Cookies are, of course, how the browser can tell who you are. Cookies are usually stored as hashes, rather than the actual cookie value, so having the hash doesnt let you impersonate the target user. Furthermore, most modern web frameworks rapidly cycle cookies, so they are only valid for a brief 10 to 15 minute window anyway.
PUBG is, in its way, the scariest zombie movie Ive ever seen, though it lacks a single zombie. It dispenses with the pretense of a story, so you can realize much sooner that the zombies, as terrible as they may be, are nowhere as dangerous to you as your fellow man.
I apologize for not blogging much in 2017. Ive certainly been busy with Discourse which is actually going great; we grew to 21 people andgave $55,000 backthis year to the open source ecosystem we build on. But thats no excuse. The truth is that its been hard to write because this has been a deeply troubling year in so many dimensions for men, for tech, for American democracy. Im ashamed of much that happened, and I think one of the first and most important steps we can take is toembrace explicit codes of conductthroughout our industry. I also continue to believe, if we start to think more holistically about what our software can do toserve all people, not just ourselves personally (or, even worse, the company we work for) that software can and should be part of the solution.
The technology described in Black Mirror can be fanciful at times, but several episodes portray disturbingly plausible scenarios withtodaysscience and tech, much less what well have 20 to 50 years from now. These are very real cautionary tales, and some of this stuff is well on its way toward being realized.
I would characterize my state of mind for the last six to eight months as poor. Not only because ofcurrent events in the United States, though the neverending barrage of bad news weighs heavily on me, and I continue to be profoundly disturbed by the erosion of core values that I thought most of us stood for as Americans. Didnt we used to look out for each other, care about each other, and fight to protect those that cant protect themselves?
All users must have a minimum password length of 10 characters.

Ive seen guidance that said you should set the overall work factor high enough that hashing a password takes at least 8ms on the target platform. It turns outSam Saffron, one of my Discourse co-founders, made a good call back in 2013 when he selected the NIST recommendation ofPBKDF2-HMAC-SHA256and64k iterations. We measured, and that indeed takes roughly 8ms using our existing Ruby login code on our current (fairly high end, Skylake 4.0 Ghz) servers.
To mitigate this threat, weve slowly tightened restrictions around Discourse backups in various ways:
Im here to report thatthe future is now.
In my extended review at Reference Home Theater, I call it the best looking TV Ive ever reviewed. But we arent alone in loving the E6. Vincent Teoh at HDTVtest writes, Were not even going to qualify the following endorsement: if you can afford it, this is the TV to gavethe E6 OLEDthe highest score of any TV the site has ever mawarded it a 9.9 out of 10, with only the LG G6 OLED (which offers the same image but better styling and sound for $2,000 more) coming out ahead.
I was provided two sets of password hashes from two different Discourse communities, containing 5,909 and 6,088 hashes respectively. Both used the PBKDF2-HMAC-SHA256 algorithm with a work factor of 64k. Using hashcat, my Nvidia GTX 1080 Ti GPU generated these hashes at a rate of ~27,000/sec.

Were gonna use the biggest, baddest single GPU out there at the moment,the GTX 1080 Ti. As a point of reference, for PBKDF2-HMAC-SHA256 the 1080 achieves 1180 kH/s, whereas the 1080 Ti achieves 1640 kH/s. In asinglevideo card generation the attack hash rate has increased nearly 40 percent. Ponder that.

⚠ Fair warning: please DO NOT start with season 1 episode 1 of Black Mirror! Start with season 3, and go forward. If you like those, dip into season 2 and the just-released season 4, then the rest. But humor me and please at least watch the first episode of season 3.
This is a security researcher who commonly runs these kinds of audits, so all of the attacks usedwordlists, along with known effective patterns andmasksderived from the researchers previous password cracking experience, instead of raw brute force. That recovered the following passwords (and one duplicate):


Common to all discourse communities are various password requirements:
However, we also valueportability, the ability to get your data into and out of Discourse at will. This is why Discourse, unlike other forum software, defaults to a Creative Commons license. As a basic user on any Discourse you can easily export and download all your posts right from your user page.
Playing games at 1080p in my living room was already possible. But now that I have an incredible 4k displa
On the topic of unanticipated downsides to technology, there is no show more essential thanBlack Mirror. If you havent watched Black Mirror yet, do not pass go, do not collect $200, go immediately to Netflix and watch it. Go on! Go ahead!
Software is easy to change, but people … arent. So in the new year, as software developers, lets make a resolution to focus on the part wecanchange, and keep asking ourselves one very important question:how can our software help people become the best version of themselves?

That was the not-so-secret design philosophy behind Stack Overflow, thatby helping others become better programmers, you too would become a better programmer. Its unavoidable. And, even better, if we leave enough helpful breadcrumbs behind for those that follow us,we collectively advance the whole of programming for everyone.
After a few hours in, I had major flashbacks tothe first time I played Counter-Strike in 1998. I realized thatwe are witnessing the birth of an entirely new genre of game: the Battle Royale. I absolutely believe that huge numbers of people will still be playing some form of this game 20 years from now, too.
As a site owner, you can easily back up and restore your entire site database from the admin panel, right in your web browser. Automated weekly backups are set up for you out of the box, too. Im notthe worlds foremost expert on backupsfor nothing, man!
Eventually the circle becomes so small that its impossible for the handful of remaining survivors to avoid contact, and one person,oneout of the hundred that originally dropped out of the cargo plane, emerges as the winner. Ive never won solo, but I have won squad, and even finishing first out of 25 squads is an unreal, euphoric experience. The odds are so incredibly against you from the outset, plus you quickly discover that 85% of the game is straight up chance: someone happens to roll up behind you, a sniper gets the drop on you, or you get caught in the open with few options. Wrong place, wrong time, game over. Sucks to be you.
Thus, the only real protection you can offer your users is just how resistant to attack your stored password hashes are. There are two factors that go into password hash strength:
Programmers dont think of themselves as people with the power to change the world. Most programmers I know, including myself, grew up as nerds, geeks, social outcasts. Did I ever tell you about the time I wrote a self-destructing Apple // boot disk program to let a girl in middle school know that I liked her? I was (and still am) a terrible programmer, but oh man did I ever test the heck out ofthatcode before copying on to her school floppy disc. But I digress. What do you do when you wake up one day and softwarehaskind of eaten the world, andit is no longer clear if software is in fact an unambiguously good thing, like we thought, like everyone told us like wewanted it to be?

Its been a while since I wrote a blog post, I guess in general, but also a blog post about video games. Video games are probablythe single thing most attributable to my career as a programmer, and everything else Ive done professionally after that. I still feel video games are one of the best ways to learn and teach programming,if properly scoped, and furthermore I takemany cues from video games in building software.
What happened to everyone? Where did they go? The sense of apocalypse is overwhelming. Its you versus the world, but where did the rest of the world go? Youll wander this vast deserted island, scavenging for weapons and armor in near complete silence. Youll hear nothing but the wind blowing and the occasional buzzing of flies. But then, suddenly the jarring pak-pak-pak of gunfire off in the distance, reminding you that other people are here. And they arent your friends.

Note that this is an intentionally tiny amount of work, its only guessing three digits. And sure enough, we cracked it fast! See the password there on the end? We got it.

And you know why I do it? I need that help, too. I get tired, angry, upset, emotional, cranky, irritable, frustrated and I need to be reminded from time to time to choose to be the better version of myself. I dont always succeed. ButI want to. And I believe everyone else for some reasonable statistical value of everyone else fundamentally does, too.
Using common password lists and masks, I cracked 39 of the 11,997 hashes in about three weeks, 25 from the community and 14 from the community.
./h64 -a 3 -m 10900 .\one-hash.txt 0234567?d?d?d
In times like these, I sometimes turn to video games for escapist entertainment. One game in particular caught my attention because of its meteoric rise in player count over the last year.
Although you can play in squads (and I recommend it), the purest original form of the game is 100 players, last man standing. You begin with nothing but the clothes on your back, in a cargo aircraft, flying over an unknown island in a random trajectory.
[advertisement] At Stack Overflow, we put developers first. We already help you find answers to your tough coding questions; now let us help youfind your next job.
sha256:64000:ZWVhZWQ4YjZmODU4Mzc0M2E2ZDRlNjBkNjY3YzE2ODA=:93LlpbKZKficWfV9jjQNOSp39MT0pDPtYx7/gBLl5jw=:0234567890
Hashcat requires the following input file format: one line per hash, with the hash type, number of iterations, salt and hash (base64 encoded) separated by colons:
Meanwile, that huge cargo airplane still roars overhead every so often, impassive, indifferent, occasionally dropping supply crates with high powered items to fight over. Airstrikes randomly target areas circled in red on the map, masking footfalls, and forcing movement while raining arbitrary death and terror.
You definitely learn to be careful, but theres only so careful you can be. Death comes quickly, without warning, and often at random. What else can you expect from a game mode where there are 100 players but only 1 eventual winner?
But all digit passwords are easy mode, for babies! How about somerealpasswords that use at least lowercase letters, or lowercase + uppercase + digits?
Lets assume for the sake of argument that this is a fully public site and nobody was posting anything particularly sensitive there. So were not worried, at least for now, about trade secrets or other privileged information being revealed, since they were all public posts anyway. If we were, thats a whole other blog post I can write at a later date.
Now that we know it works, lets get down to business. But well start easy. How long does it take to brute force attackthe easiest possible Discourse password, 8 numbers thats only 108combinations, a little over one hundred million.

After this exercise, I now have a much deeper understanding of our worst case security scenario, a database compromise combined with a professional offline password hashing attack. I can also more confidently recommend and stand behind our engineering work in making Discourse secure for everyone. So if, like me, youre not entirely sure you are doing things securely, its time to put those assumptions to the test. Dont wait around for hackers to attack you hacker, hack thyself!
Battle Royale is not the game mode we wanted, its not the game mode we needed, its the game mode we alldeserve. And the best part is, when were done playing, we can turn it off.
Users cannot use any password matching a blacklist of the 10,000 most commonly used passwords.
If we want Discourse to be nation state attack resistant, clearly well need to do better. Hashcat has a handy benchmark mode, andheres a sorted list of the strongest (slowest) hashes that Hashcat knows aboutbenchmarked on a rig with 8 Nvidia GTX 1080 GPUs. Of the things I recognize on that list,bcrypt,scryptandPBKDF2-HMAC-SHA512stand out.
Guess.Mask…….: ?l?l?l?l?l?l?l?l [8] Time.Estimated…: Mon Sep 04 10:06:00 2017 (94 days, 10 hours) Guess.Mask…….: ?1?1?1?1?1?1?1?1 [8] (-1 = ?l?u?d) Time.Estimated…: Sun Aug 02 09:29:48 2020 (3 years, 61 days)
That used to sound all hip and cool and inspirational, like Wow! We software developers reallyaremaking a difference in the world! and now for the life of me I cant read it as anything other than an ominous warning that we just werent smart enough to translate properly at the time. Butmaybe now we are.
⚠️ Thats why, if you know (or even suspect!) your database was exposed, the very first thing you should do is reset everyones password.
Which reminds me ofanother joke that people were telling in 2015:
The issue is bigger than any single scandal, I told him. As headlines have exposed the troubling inner workings of company after company, startup culture no longer feels like fodder for gentle parodies about ping pong and hoodies. It feels ugly and rotten. Facebook, the greatest startup success story of this era, isnt a merry band of hackers building cutesy tools that allow you to digitally Poke your friends. Its a powerful and potentially sinister collector of personal data, a propaganda partner to government censors, and an enabler of discriminatory advertising.
Donald Trump is basically a comment section running for president
Dont believe me? Well, guess which display in the below picture is OLED? Go on, guess:
But what if youdontknow? Should you preemptively reset everyones password every 30 days, like the worlds worst bigco IT departments? Thats downright user hostile, and leads to serious pathologies of its own. The reality is that you probablywontknow when your database has been exposed, at least not until its too late to do anything about it. So its crucial to slow the attackers down, to give yourself time to deal with it and respond.
I didnt choose to be a programmer. Somehow, it seemed,the computers chose me. For a long time, that was fine, that was enough; that was all I needed. But along the way I never felt that being a programmer was thisunambiguously great-for-everyonecareer field with zero downsides. There are absolutely occupational hazards of being a programmer, andone of my favorite programming quotesis an allusion to one of them:
Over the years, weve learned that balancing security and data portability can be tricky. You bet your sweet ASCII afull database downloadis what hackers start working toward the minute they gain any kind of foothold in your system. Its the ultimate prize.
A brute force try-every-single-letter-and-number attack is not looking so hot for us at this point, even with a high end GPU. But what if we divided the number byeightby putting eight video cards in a single machine?Thats well within the reach of a small business budget or a wealthy individual. Unfortunately, dividing 38 months by 8 isnt such a dramatic reduction in the time to attack. Instead, lets talk about nation state attacks where they have the budget to throwthousandsof these GPUs at the problem (1.1 days), maybe eventens of thousands(2.7 hours), then yes. Even allowing for 10 character password minimums, you are in serious trouble at that point.
The work factorornumber of iterations. Set this as high as possible, without opening yourself up to a possible denial of service attack.

The name of the security game is defense in depth, so all these hardening steps help but we still need toassume that Internet Bad Guys will somehow get a copy of your database. And then what? Well, whats in the database?